Microsegmentation – What is it and how does it work?


Microsegmentation – What is it and how does it work? What does it offer and why is it gaining increasing attention? This blog article has all the answers to all these questions and more.
Network security is of utmost importance in today’s digital age. With the increasing amount of sensitive information shared and stored online, the number of cyber attacks multiplied, with data and systems in danger of being stolen or damaged.
Therefore, enhancing security has become a primary goal for individuals, companies, and network administrators.
One greatly useful network security technique is microsegmentation. In this article, we will cover what it is, explore its benefits and explain how the eTag Fuse platform can boost security for organizations.
What is Microsegmentation?
Microsegmentation involves dividing a network into smaller, isolated segments or zones called microsegments. Each microsegment acts as a separate security perimeter, isolating specific sets of resources and controlling access between them.
In other words, each segment in the network is treated as a separate entity, a feature that allows businesses to implement individualized security policies and controls based on the specific needs of each segment.
Why is Microsegmentation needed?
You might wonder what microsegmentation brings to the table. And the answer is that instead of security policies applied at a broader level, such as firewalls and intrusion detection systems (IDS), microsegmentation provides a higher level of security.
Traditional networks were divided into larger segments or subnets, an approach that allowed for broader access within each segment. Whilst making it easier for attackers to move laterally across the network if they gained access to one segment.
Microsegmentation addresses this limitation by creating smaller and more granular segments, typically at the application or workload level. In such a network, each segment can have its own set of security policies, such as access controls, traffic filtering, and monitoring.
By segmenting the network into smaller zones, businesses can create a more granular security model, which allows them to control access to critical resources more effectively.
Security policies can be applied to each microsegment, specifying which resources are allowed to communicate with each other. This level of segmentation allows organizations to implement a zero-trust security model, where access to resources is only granted on a need-to-know basis, regardless of whether the resources are in the same subnet or physical location.
How does Microsegmentation work?
Microsegmentation divides a network into smaller segments, viewed as individual zones. Each zone is protected by its own security policies and controls, allowing a more tailored approach to security.
Microsegmentation can be implemented using various network virtualization technologies, such as software-defined networking (SDN), virtual local area networks (VLANs), and next-generation firewalls (NGFW).
Virtualization allows businesses to create virtualized zones that can be managed independently of physical network resources. SDN provides a flexible and programmable way to create network segments. NGFW allows businesses to implement granular security policies at the application level, while VLANs are capable to create smaller network segments that virtually connect hosts.
Regardless of the technology employed, microsegmentation requires a clear understanding of the network’s topology and the types of traffic that flow through it. By analyzing network traffic patterns, businesses can identify the most critical assets and create security policies that protect them.
Why is Microsegmentation important?
Microsegmentation boosts network security by creating a more granular security model that can protect critical assets more effectively.
By dividing the network into smaller zones, businesses limit the impact of an eventual security breach by containing it within a single segment. This approach also makes it more difficult for hackers to move laterally across the network, as they would in a traditional network. In a microsegmented network, they would need to compromise multiple segments to gain access to critical resources.
Not only that, but microsegmentation can help businesses comply with various regulatory requirements such as the General Data Protection Regulation (GDPR) and the Health Insurance Portability and Accountability Act (HIPAA).
These are regulations that require businesses to implement robust security measures to protect sensitive data. With microsegmentation, companies can meet such requirements much easier and in a more effective way.
Benefits of Microsegmentation
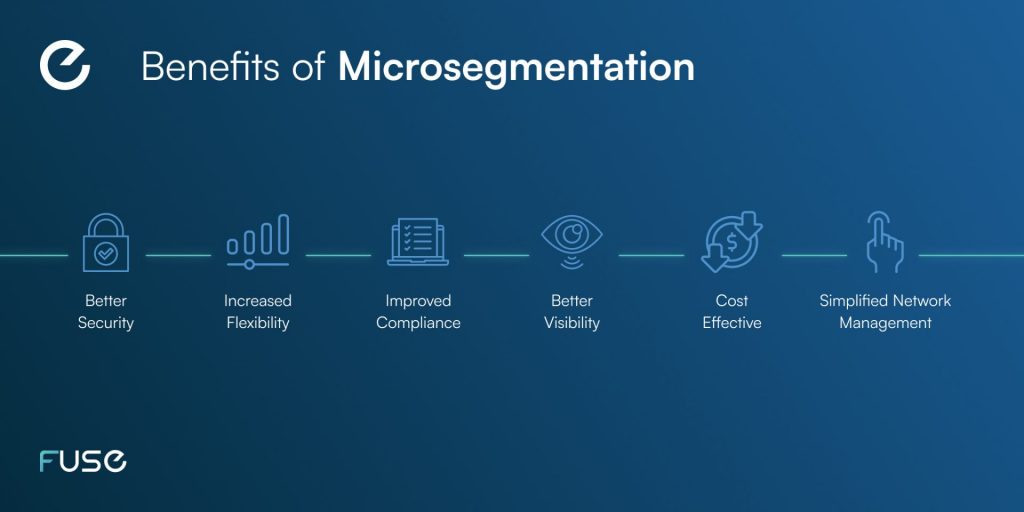
Many aspects make microsegmentation appealing to businesses. We listed them below:
1. Better Security
Where else to start? Microsegmentation provides a higher level of security than traditional network security methods, as it allows businesses to create a more tailored approach to security. With individualized security policies and controls for each segment, businesses can protect critical assets more effectively and limit the impact of a possible security breach.
2. Increased Flexibility
Microsegmentation provides businesses with more flexibility in terms of network management and control. By dividing the network into smaller segments, businesses can create more agile and responsive networks that adapt to changing business needs.
3. Improved Compliance
Microsegmentation can help businesses comply with various regulatory requirements, such as GDPR and HIPAA. By implementing robust security measures such as microsegmentation, businesses can protect sensitive data and avoid costly fines and penalties.
4. Better Visibility
Microsegmentation can provide businesses with better visibility into their networks, allowing them to identify potential security threats quicker. By monitoring traffic patterns within each segment, businesses can detect unusual behavior and take appropriate action to prevent a security breach.
5. Cost-Effective
Microsegmentation can be a cost-effective way to improve network security, as it allows businesses to focus their resources on protecting critical assets. By segmenting the network into smaller zones, businesses can reduce the cost of implementing security policies and controls across the entire network.
6. Simplified Network Management
Microsegmentation can simplify network management by allowing businesses to manage each segment independently. This approach can make it easier to troubleshoot network issues and implement changes to a specific network area, without affecting other segments.
Challenges of Microsegmentation
We saw what makes microsegmentation appealing, but are there any shortcomings of the technology?
Naturally, it has its challenges, such as:
1. Complexity
Microsegmentation implementation can be a complex process, especially in large and complex networks. It requires a deep understanding of the network topology and traffic patterns, as well as the ability to configure and manage multiple security policies and controls.
2. Scalability
Microsegmentation can be challenging to scale, especially as the network grows in size and complexity. Businesses must ensure that their microsegmentation strategy can accommodate future growth and changing business needs.
3. Resource Requirements
Microsegmentation requires significant resources, including specialized hardware and software, as well as skilled personnel to manage and maintain the network. This might be a burden for smaller businesses or those with limited resources.
4. Maintenance
Maintaining a microsegmented network can be challenging, as it requires ongoing monitoring and maintenance to ensure that security policies and controls are up-to-date and effective. This can be a time-consuming process, especially in large and complex networks.
Best practices for Microsegmentation
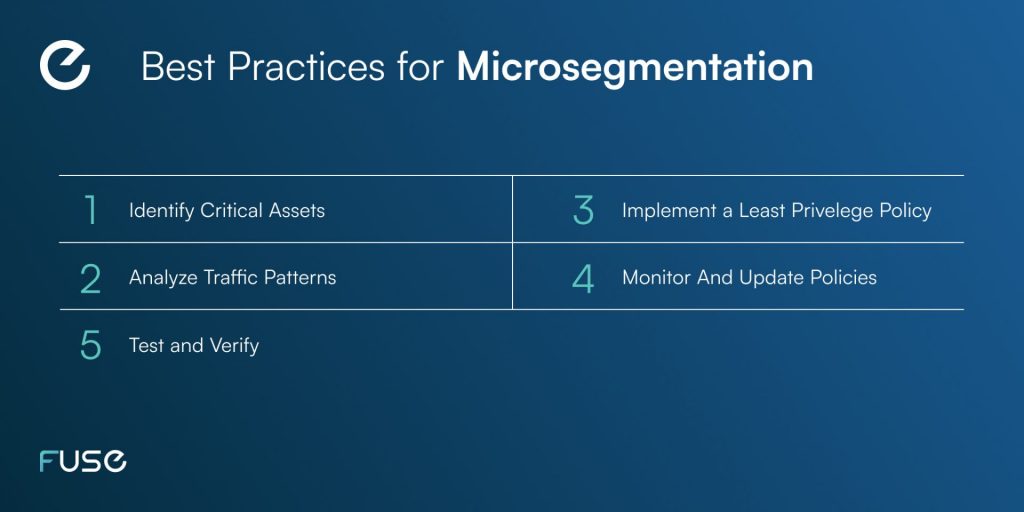
To ensure the microsegmentation strategy is successful, there are some best practices to follow:
1. Identify Critical Assets
Businesses should start by identifying their critical assets and determining which segments they should protect. This can help create a more targeted and effective microsegmentation strategy.
2. Analyze Traffic Patterns
To create effective security policies and controls, businesses must understand the types of traffic that flow through each segment. An analysis of traffic patterns helps businesses reveal potential security threats and create policies that protect against them.
3. Implement a Least Privilege Policy
Microsegmentation should follow a least privilege policy, which means that each segment should only have access to the resources and services it needs to perform its function. This can help prevent lateral movement across the network and limit the impact of a security breach.
4. Monitor and Update Policies
Microsegmentation requires ongoing monitoring and updating to ensure that security policies and controls are up-to-date and effective. Businesses should establish a regular schedule for reviewing and updating policies and rules, and ensure that personnel responsible for managing the network have the necessary skills and resources to do so.
5. Test and Verify
Before implementing microsegmentation, it is essential to test and verify the strategy to ensure that it is effective and does not disrupt normal network operations. This can help prevent downtime and other issues that can result from an ineffective microsegmentation strategy.
Can Microsegmentation be applied to an identity provider?
Microsegmentation can be applied to an identity provider (IdP) with features that enable authorization and limit access to resources, and it can help improve the security and efficiency of an organization’s Identity and Access Management (IAM) system.
An IdP typically manages access to resources and applications by verifying the identity of users and providing authorization based on pre-defined policies.
Microsegmentation can help improve security within an IdP by dividing the network into smaller segments based on factors such as user roles, applications, and locations. This can help ensure that access to sensitive resources is limited only to those who have the necessary permissions.
For example, an IdP may be segmented based on the type of user accessing the system. Different types of users may have different levels of access to resources based on their role within an organization.
Microsegmentation can help ensure that users only have access to the resources that they need to perform their job, and not to resources that are unnecessary or potentially harmful.
How can Fuse help with Microsegmentation?
As mentioned before, microsegmentation has its challenges, and its implementation could be tricky for some.
The good news is, we have a solution. Our digital enablement platform, eTag Fuse, simplifies microsegmentation for you. One of its key features is that it provides granular access controls, which are essential for micro-segmentation. The platform allows organizations to define policies that limit access to specific resources based on factors such as user identity, location, and time of day.
This level of granularity helps organizations ensure that only authorized users have access to sensitive resources, which can significantly reduce the risk of data breaches.
Fuse also offers a comprehensive set of identity management capabilities. This includes user provisioning, deprovisioning, and access management, as well as support for multi-factor authentication (MFA) and single sign-on (SSO). These features help organizations streamline their Identity and Access Management (IAM) processes and reduce the burden on IT teams.
In conclusion
The eTag Fuse platform solves the scalability problem, being suitable for organizations of all sizes. The platform can easily accommodate thousands of users and devices, making it ideal for large enterprises. Additionally, the platform is designed to integrate with existing security infrastructure, such as firewalls and intrusion detection systems, which helps organizations improve their overall security posture.
In addition, the eTag Fuse platform offers advanced analytics and reporting capabilities. This allows organizations to gain insights into user behavior and identify potential security risks. The platform generates detailed reports that highlight trends and anomalies, allowing organizations to proactively address security issues before they become a problem.
Finally, the eTag Fuse platform is a powerful solution that offers advanced IAM and identity management capabilities in the context of micro-segmentation. Its granular access controls, comprehensive identity management features, scalability, and analytics capabilities make it an ideal solution for organizations looking to improve their security posture and streamline their IAM processes.
Contact us today to learn more about how eTag Fuse can help your organization!